How to Ensure Security in Your Oracle APEX Application Development Project?

Oracle APEX is a powerful low-code development platform that enables businesses to build custom applications quickly and efficiently. Again, security is one of the top most concerns that organizations have when it comes to Oracle APEX Application Development Services.
But what should be the critical factors for developing a secure solution? Every organization is unique, and security requirements will vary in different environments. In this blog post, we’ll explore some best practices for ensuring security in your Oracle APEX application development project.
Securing Oracle APEX Application Development Services
-
Using SSL
Oracle APEX is a web application development framework that allows you to build database-driven applications. Oracle APEX supports various programming languages, including Java, JavaScript, JSP and PHP. Use SSL certificates for your server and client applications to ensure security in your Oracle APEX application development project.
SSL stands for Secure Sockets Layer, a protocol that encrypts data between the browser and server using symmetric encryption keys. An SSL certificate on your server automatically encrypts the data sent between your browser and server so that no one can intercept or alter it without the correct key.

Using an SSL certificate on your browser (for example, Microsoft Internet Explorer) and the server where you are developing your application will make it much more secure for your users to access information from the database.
-
APEX Advisor
The Oracle APEX Advisor is a built-in analysis tool and a great way to ensure your project is secure and compliant. It helps you identify issues with your code and check for insecure practices such as default passwords, SQL injection attacks, and the like.
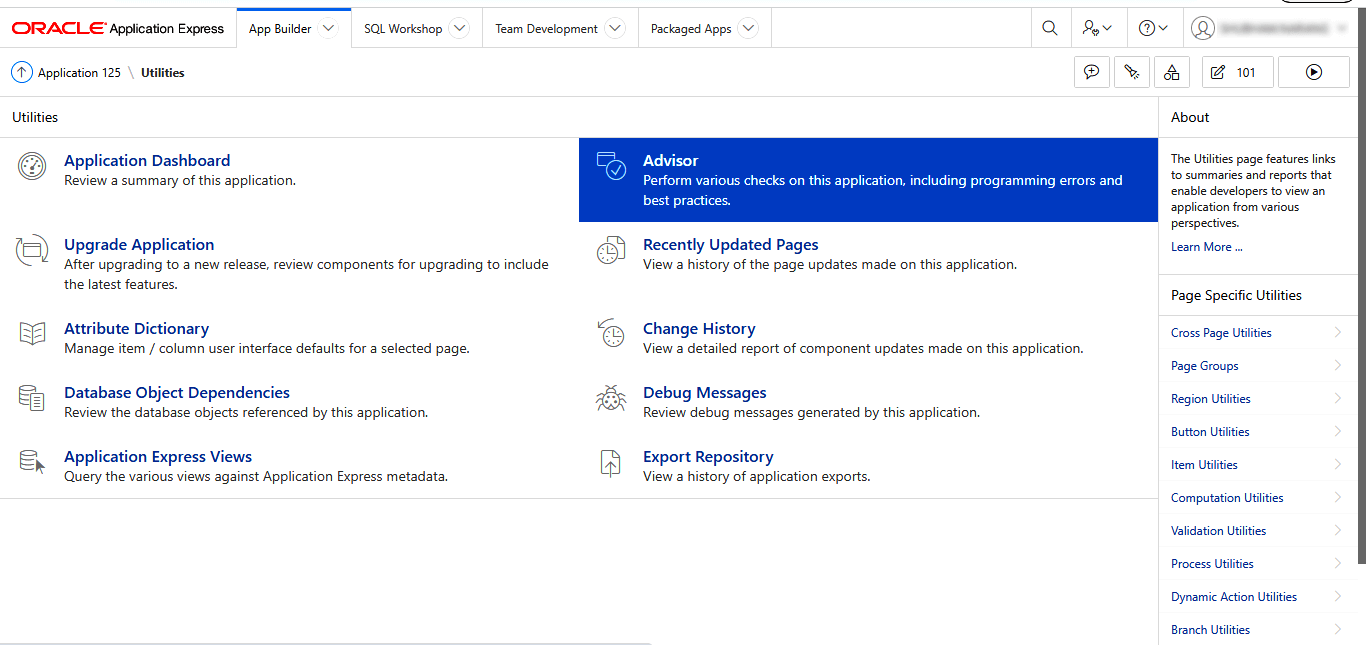
This tool also gives you insight into how insecure your application is. You can see exactly what kind of attacks are possible and how likely they will succeed against this application. It’s a good idea to run this analysis when developing an application to understand how vulnerable it is to attack.
-
Follow Secure Development Practices
You will work with a lot of data and information as an application developer. This means that proper security is a must for your projects, and the best way to ensure this is by following secure development practices.
These are the steps that you can follow:
- Create a Comprehensive Threat Model:
The first step in secure APEX development is establishing a comprehensive threat model for your application. The threat model should include all the risks affecting your application, including cyber attacks and malicious code. - Create a Secure Development Lifecycle (SDLC) Plan:
Once you have established your threat model and have determined which areas need to be secured, you will need to create an SDLC plan for securing those areas. This includes defining what security controls you will use when they should be implemented, who will implement them and how frequently they will be updated. It’s also important to keep your code up to date with the latest security patches and updates. - Implement Security Controls in Both Design and Code:
Security controls are any mechanisms, such as encryption, authentication, access control lists (ACLs), and other mechanisms that can be used to protect a system from unauthorized access. This includes using parameterized SQL queries to prevent SQL injection attacks, validating user input to prevent cross-site scripting (XSS) attacks, and avoiding the use of eval() or similar functions that can introduce security vulnerabilities. These security controls must be implemented throughout the application development lifecycle. In particular, they must be implemented during design time and testing time. - Follow the Principle of Least Privilege:
The principle of least privilege is a fundamental security principle that states that users and processes should only be granted the minimum level of access necessary to perform their tasks. This principle should be applied throughout your Oracle APEX application development services, including the design of user roles and privileges, the configuration of database access, and the implementation of security features like encryption and hashing. - Test Your Application for Vulnerabilities:
The best way to find vulnerabilities in your application is to use automated tools. These tools can also be used to test the application for security vulnerabilities. Such tools include static analysis, dynamic analysis and fuzzing. Static analysis is a technique that looks at the source code and finds potential vulnerabilities. Dynamic analysis is a technique that uses profiling techniques to look at the running system and find out whether any threats exist or not. Fuzzing is a method of testing applications by injecting malformed data into them to discover security issues. These methods are beneficial in finding security issues in an application before they become a severe threat.
To Wrap Up
Ensuring security in your Oracle APEX application development project requires a comprehensive and multi-faceted approach that addresses all aspects of the development process, from design and coding to testing and compliance. By following best practices like those outlined above, you can minimize the risk of security vulnerabilities and ensure that your application is secure, reliable, and compliant with industry standards and regulations.
You can trust Abaca Systems for tailored and secure Oracle APEX application development services. We have been developing and delivering Oracle APEX applications for over a decade.
Our team of expert developers, consultants, and system integrators are experts in their respective fields and can create a wide range of applications from small to enterprise level using APEX.
